Topics
- All Asana features
- Set up your ideal workspace
- You’ve been invited to Asana; now what?
- Top features to discover
- Getting started with Asana’s mobile app
- Navigating Asana
- Create projects in Asana
- How to use Asana help resources
- Different types of tasks
- New navigation in Asana
- Quick-start guide to Asana
- Collaborating in Asana
- Create tasks in Asana
- Asana desktop app
- How Asana works
- Structure your projects clearly
- Stay informed with your Asana Inbox
- Manage and prioritize your tasks
- Comments, messages, and status updates
- Automate and scale your work with the Customize menu
- Assign tasks to teammates
- Powerful Asana features for work management
- Find work fast with search
- Create projects quickly with templates
- Maximize productivity with My tasks
- Connect your tools with Asana
- Plan and execute projects with a deadline
- Top Asana integrations
- Monitor initiatives and track work with portfolios and dashboards
- How to invite team members to Asana
- Setting and tracking progress towards goals
- Asana for team leads
- How to choose the right project blueprint for your work
- Reporting with dashboards
- Reporting with workload
- Customize your projects and portfolios
- Planning with Asana calendar
- Tracking project progress
- Share project updates
- Make the most of your Asana trial
- How to cancel your Asana trial
- My trial has ended, what happens to my tasks, rules, and workflows?
- How to add payment details to a trial
- Purchasing a subscription after a trial
- Turn your trial into a paid plan
- Set goals during your Asana trial
- Invite others during your trial
- How to sign up for a free Asana trial
- What is a workflow?
- Add movement to your workflow
- Multi-home tasks to avoid information silos
- Assign work automatically with custom fields
- Building cross-functional workflows in Asana
- Moving your everyday workflows to Asana
- Schedule tasks based on priority
- Build the foundation of your workflow
- Automate how work moves through stages
- Request a task review with a simple automation
- Use dependencies to kick work off at the right time
- Control how tasks are added to projects
- How to export all time entry data from Asana as CSV via API
- Formula custom fields
- Bundles
- Custom fields
- Conditions and branching in rules
- Dependency types
- Auto-shifting dates for dependent tasks
- Rules integrations for cloud storage and file sharing
- Rules integrations for productivity and communication
- Custom field types and limitations
- Rule actions
- Rule permissions
- Filtering and sorting custom fields
- Sharing a form
- Manual rule triggers
- Setting dates in rules
- PagerDuty rules integration
- Management dashboard for global fields
- HubSpot rules integration
- Bundle management and permissions
- Bundles FAQ
- Reference custom fields
- Workflow builder
- Rules integrations and widgets
- Management dashboard for project templates
- ID custom fields
- Applying bundles to projects
- Field mapping in forms
- Email communication with form submitters
- Rule triggers
- Rule execution history
- Form customization
- Variables in rules
- Forms
- Project templates
- Status updates templates
- Task Templates
- Time tracking in Asana
- Rules
- Task dependencies
- Approvals
- Asana app in Claude
- Migrating time tracking data from Everhour to Asana
- Calendars and Asana
- Zoom meetings in Asana
- GitHub and Asana integration
- Microsoft Teams and Asana integration
- Zapier and Asana
- Vimeo and Asana
- Power BI integration
- Google Calendar + Asana
- Google Sheets & Asana
- Instagantt + Asana
- How to create a Zoom call notes workflow with AI Studio
- Zoom transcripts for automation and AI Studio
- Zendesk integration
- Asana in Salesforce AppExchange (being deprecated)
- Wufoo and Asana
- Asana and Workplace from Meta
- Jira Data Center FAQ
- Outlook Calendar and Asana
- Tray.io + Asana
- Web forms & Asana
- Splunk + Asana
- Asana app in ChatGPT
- Asana for Adobe Creative Cloud
- Jira Data Center
- Google Forms and Asana
- Compliance management: API and integration support
- Asana for Gmail add-on
- Google and Asana
- Google Smart Chips
- Asana for Jira Cloud FAQ
- Chrome Extension + Asana
- Salesforce in Asana integration
- ServiceNow & Asana
- Enabling permissions for Asana-built and Microsoft 365 integrations
- Asana for Tableau integration
- Asana for Jira Cloud
- API
- Slack and Asana
- Asana for Outlook add-in
- Progress, status, and connecting work to goals
- Goal types and templates
- Goals strategy map
- Write great goals with Asana Goals
- Get started with Asana Goals
- The goal tracking process with Asana Goals
- Lead the goals management process in your organization with Asana Goals
- Weighted goals
- Goals privacy and sharing
- Viewing and filtering your goals
- Asana Goals FAQ
- Text formatting in Asana
- Task fields
- Email tasks to Asana
- Rules in My tasks
- Task actions
- My Tasks
- Scheduling tasks using start dates, due dates, and times
- Proofing
- Save time in Asana
- Subtasks
- Understanding tasks
- Task comments and attachments
- Views in My tasks
- Custom fields in My tasks
- Converting tasks into projects
- Custom task types and statuses
- Tags
- Shareable notes in Asana
- Timeline
- Understanding projects
- Calendar view
- Import data from other tools to projects in Asana
- List view
- Managing tasks and dependencies with timeline
- Sections
- Advanced CSV import options
- Critical path on timeline
- Project owner and members
- Gantt view FAQ
- Files view
- Project overview tab
- Board view
- Embedded media project view
- Gantt view
- Project importing and exporting
- Preparing data for CSV import
- Teamless projects
- Notes view
- Project customization and views
- Project permissions
- Individual project permissions
- Team permissions
- Private custom fields
- Edit restriction on custom field values
- Project privacy settings
- Asana custom field permissions
- Team content permissions for team admins
- Viewer project access level
- Project admin access level
- Domain-wide admin controls
- Read-only links
- Permissions overview
- Editor access level
- Custom field access levels
- Sharing and limiting access to teams
- Team sharing
- Task permissions
- Forms access permissions
- Asana for Agile and Scrum
- Project intake
- Asana for team meetings
- Giving feedback and approvals
- How to apply a RACI Matrix in Asana
- Pipelines
- Plan and manage company goals
- Organizational strategic planning
- Resource planning
- Ideas and brainstorms
- End-of-month close processes for Finance teams
- One-on-ones
- Using Asana to track customer feedback
- Using Asana for project management
- How to use Asana for account tracking
- Event planning with Asana
- Creative production
- Campaign management
- Managing design feedback and critique meetings
- Using Asana for your product roadmap
- Asana for Sales and Account Management teams
- Video production calendar
- How to create a content calendar in Asana
- Marketing strategic planning
- AI add-on beta services
- Get started with AI Teammates
- Asana AI features and admin controls
- Sharing feedback on AI features
- Smart projects
- Smart editor
- Smart summaries
- Asana AI FAQ
- Smart fields
- Smart goals
- Asana AI customization
- Smart import
- Smart rule creator
- Smart status
- Managing your AI Teammates Add-On Licenses
- AI Teammates
- Triggering AI Teammates
- Smart chat
- Get started with Asana AI
- Understanding access control, memories, and approvals for AI Teammates
- AI Studio credit optimization
- Work smarter with Asana AI
- Create Smart workflows with AI Studio
- Writing instructions in AI Studio
- Connect your Smart workflow with the right data sources
- How to structure a prompt in AI Studio
- AI Studio pre-built AI rules
- Words to workflows in AI Studio
- AI Studio FAQ
- Troubleshooting in AI Studio
- How the Use AI variable works
- AI Studio - Human in the loop
- AI Studio Plus
- An admin's guide to AI Studio
- Introduction to Asana AI Studio
- AI Studio models
- AI Studio add-on and pricing
- eDiscovery Resource Center
- Asana Japan Data Center
- HIPAA Compliance
- Asana EU Data Centre
- Asana and Global Trade Compliance
- Privacy and security
- Accounts
- Enterprise Key Management (EKM)
- Mandatory two-factor authentication
- Two-factor authentication
- Setting up Asana roles in Okta with SCIM
- Service accounts
- Data retention policy
- Access and permissions
- Delete your Asana account
- Asana account email policy
- Multiple accounts and merging
- Setting SAML group mapping for licenses
- SAML group mapping and SCIM interaction
- Compliance management add-on
- FedRAMP Compliance
- SecureAuth for Enterprise Organizations
- Profile field editability controls
- Global authentication settings
- Automatic guest removal
- Mobile apps security permissions
- How to separate Asana accounts
- Admin security controls
- App management and integrations
- Permissions management add-on
- Managing password settings in the admin console
- IP allowlisting in Asana
- Provisioning and deprovisioning users with SCIM
- Authentication and access management options for paid plans
- Claiming admin permissions on work items
- Role-based access control (RBAC) with custom roles
- Asana IP address ranges and hostnames
- Data Residency for Asana
- Multi-org deployment
- Setting up Asana roles in Microsoft Entra ID with SCIM
- How to access the admin console
- Admin and super admin roles in Asana
- Manage approved workspaces
- University organizations
- Managing an organization
- Managing organization settings
- Managing teams through the admin console
- Managing people in organizations
- Understanding workspaces
- Workspaces and organizations FAQ
- Managing members in an organization
- Division access and management FAQ
- Advanced division management
- Managing workspaces
- Introducing Asana Gov
- Managing members and teams in a division
- A guide to divisions in Asana
- License assignment in divisions
- Asana Sandboxes
- Membership and collaboration in workspaces
- Your Asana account
- Changes to automatic payments in India due to RBI regulations
- Adding payment methods for manually invoiced customers
- Payments in MXN and BRL currency
- VAT/GST & Sales Tax
- Payments in CAD and KRW currency
- Upgrading or changing your Asana plan
- Accessing your billing page
- Iceland VAT
- Norway VAT
- Singapore GST
- Switzerland VAT
- New Zealand GST
- Indonesia VAT
- United Kingdom VAT
- South Korea VAT
- South Africa VAT
- EU VAT
- Australia GST
- United States sales tax
- Subscription management and upgrades
- Philippines VAT
- Canada GST/HST, QST, and provincial sales tax
- Payment methods and invoices
- Billing
- Billing settings in the admin console
- Security and billing for divisions
- How to cancel your Asana plan
- Divisions
- Learn about Asana Premium features
- Learn about Asana Legacy Enterprise features
- Learn about Asana Business features
- Asana for nonprofits
- Learn about Asana Starter features
- Learn about Asana Advanced features
- Modify your Asana plan
- Manage your growing Asana subscription
- Asana Personal Plan details
- Asana subscriptions and pricing
- Pricing and purchases
- View only
- Deprecation of integrations
- Troubleshooting browser and connectivity issues
- Accidental deletion
- Security and permissions
- Salesforce AppExchange Integration Deprecation FAQ
- Tasks and subtasks
- Asana Forum basics
- Asana Certification FAQ
- Upcoming discontinuation of personal projects spaces
- Navigation and display
- How do I get support from Asana?
- Recover deleted tasks, projects, and more
Enabling permissions for Asana-built and Microsoft 365 integrations
If you want to use Asana-built Microsoft 365 integrations, you may need to work with your Microsoft admins with access to Microsoft Entra (fka Azure Active Directory) to consent to the required permissions. Consenting to these permissions authorize Asana to read and/or write data in the corresponding Microsoft 365 applications so the Asana-built integrations can “talk to” these applications.
In this article, we summarize the required permissions for the Asana-built Microsoft 365 integrations and walk through several options for your Microsoft admins to turn on these permissions for you.
Required permissions by integration
|
Integration |
Required permissions |
|---|---|
|
Calendars.ReadWrite | |
|
Permissions to use Asana Bot in MS Teams:
Permissions to use MS Teams app within Asana to create Asana App rules:
Permissions for Asana Tab in MS Teams:
| |
|
Outlook Email + Asana:
| |
|
Files.Read.All |
How Microsoft admins can enable these permissions
Depending on the organizational culture, there are several ways to enable these permissions. We summarize 3 ways below, and you can find one that works best for your organization.
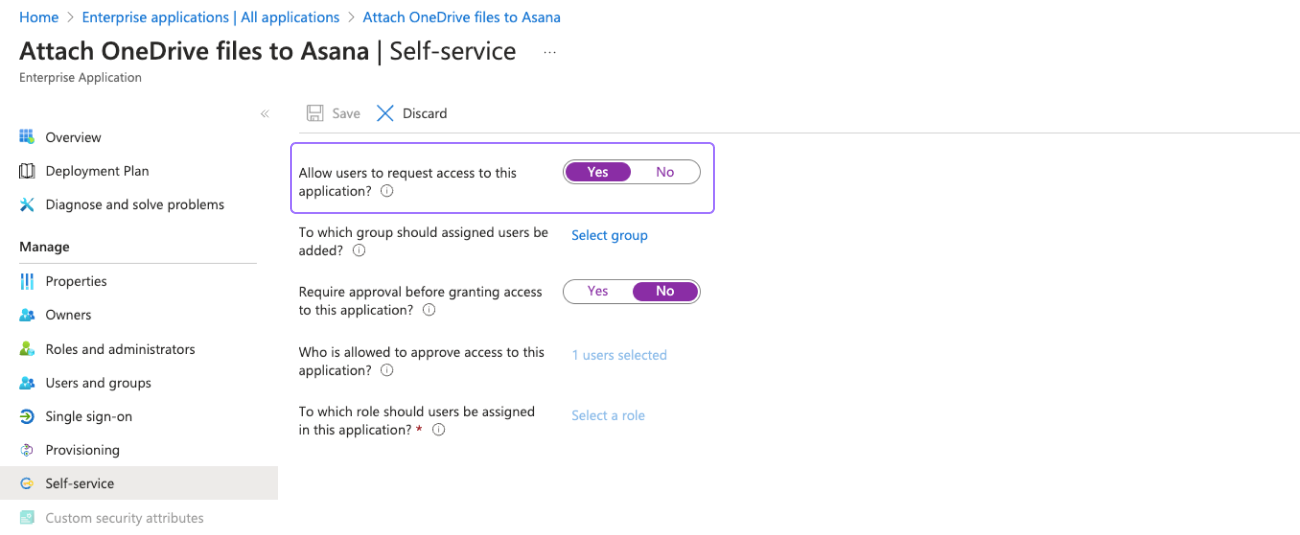
Assign users or groups to an integration
If your organization wants to have strict control over which users or groups have access to a particular Asana-built integration, your Microsoft admins can assign the integration to specific users or groups. Most organizations would prefer this approach.
- Log into Microsoft Entra > Enterprise applications
- Search and open an Asana-built integration, e.g. Asana for Outlook Email
- Click “Assign users and groups” and then “Add user/group”
- Added user(s) and group(s) are authorized the permissions to this application
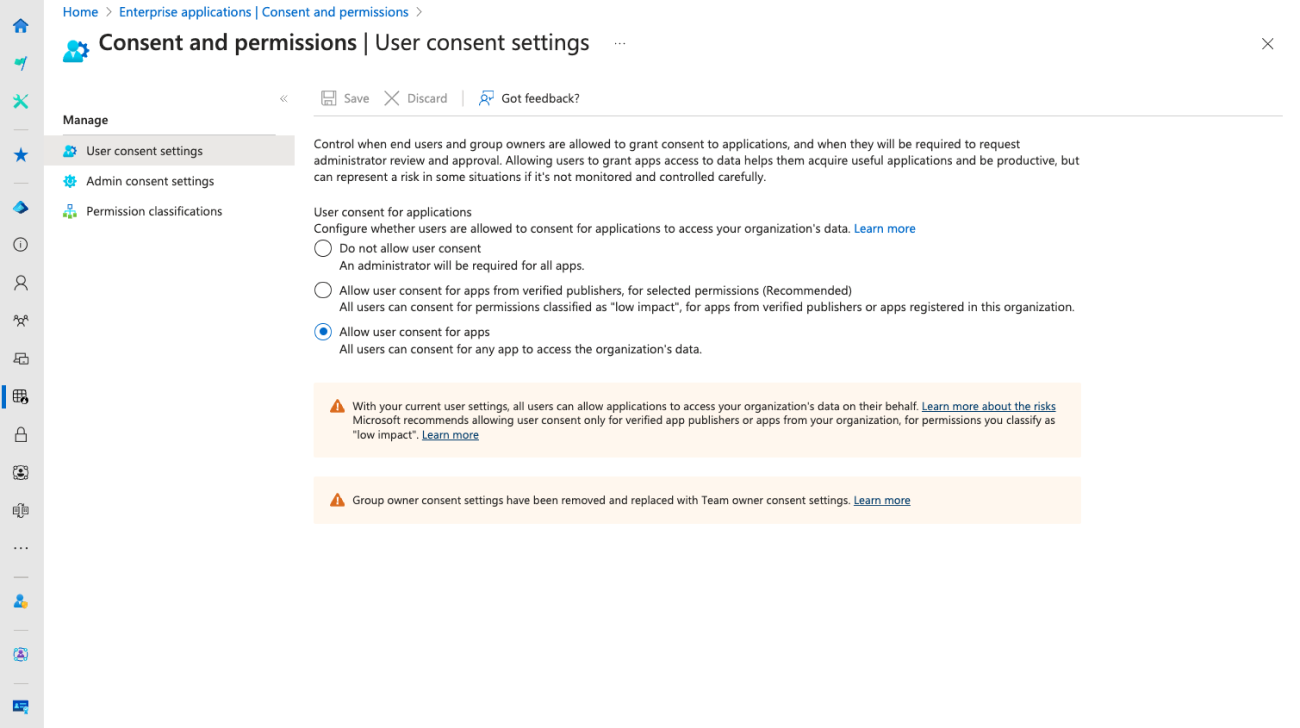
Enable “Allow user consent for apps”
If your organization encourages employees to experiment and adopt integrations that work best for their workflows, Microsoft admins can allow “user consent for apps” to give employees’ autonomy to consent to relevant permissions.
In Microsoft Entra, navigate to Enterprise applications | Consent and permissions to enable user consent. This gives your employees the flexibility to accept or decline requested permissions when they attempt to use Asana-built Microsoft integrations.
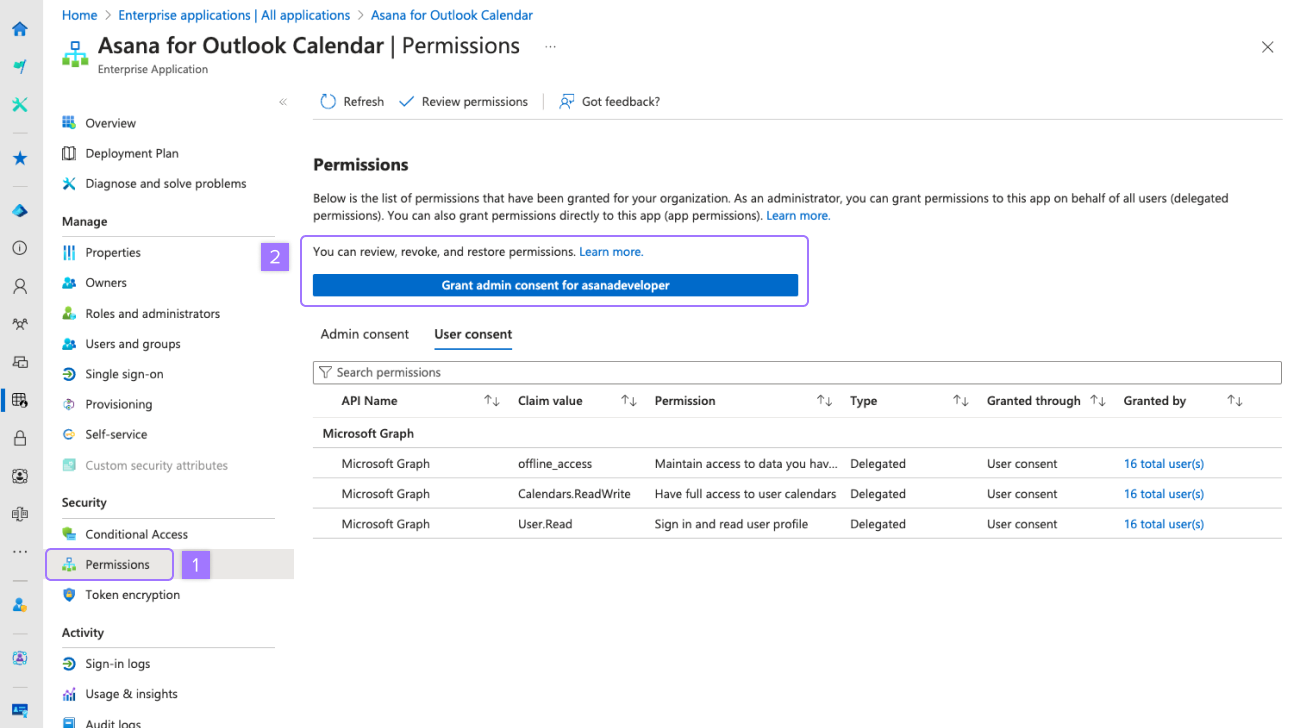
Enable “Grant admin consent”
Your Microsoft admins can also choose to grant “admin” consent to the permissions required of an Asana-built integration (e.g., Asana for Outlook Email). This would grant consent to any Microsoft 365 integrations (not just the one built by Asana) that require authorization to these permissions.
If this is the preferred approach, you can:
- Go to Microsoft Entra > Enterprise applications
- Search and open an Asana-built integration. For example, Asana for Outlook Email
- Click Permissions under the left nav bar
- Click Grant admin consent for {Your organization's domain name}